How well is your business protected when a global pandemic strikes?
If someone would’ve asked you that question 5 year ago, you might have laughed it off as far-fetched.
Today, not so much.
Figuring out how big of a risk something could be to your business and, if it happens, how significant the impact will be is probably more relevant than ever.
Risk assessment can help you streamline analyzing each potential risk a business could face.
Risks such as:
- Your employees’ health and safety in a production environment
- Food safety in the food industry
- IT safety risks when working with sensitive data or software
- Protecting your customers’ personal details
- Intellectual theft
- Fire safety management procedures
- Potential lawsuits
- A global pandemic
You can use a risk assessment in almost every business type, but what is a risk assessment exactly?
What is a risk assessment?
A risk assessment is just one part of the risk assessment process where you:
- Identify potential risk factors, either physical, digital, and anything in between.
- Analyze and evaluate the risk associated with those potential threats
- Determine how to eliminate or control the risk
The risk assessment process aims to evaluate risks and then remove or minimize their risk level by adding control measures or taking precautions.
If done successfully, you have created a safer and more secure workplace for all stakeholders.
The goal is to try to answer the following questions:
- What can happen, and under what circumstances? (Risk identification)
- What are the possible consequences? (Risk analysis)
- How likely are the potential consequences to occur? (Risk evaluation)
- Is the risk under control, or is further action required? (Risk Control)
In this article, we’ll focus on analyzing and evaluating the risk associated with those potential threats.
To find all your potential risks, you have to consider what would happen if everything that could go wrong goes wrong. But what if you’ve done that. What if you found all potential threats to your business and would like to know the likelihood and the impact of the risk happening?
Let’s build your risk assessment and find out.
How to create a risk assessment
Step 1. Identify the Hazards
Begin by identifying potential hazards that could pose risks to your project or workplace. This involves looking at all aspects of the operation and considering a wide range of factors, including physical hazards, environmental factors, human factors, and technological issues. Digital forensics plays a crucial role when assessing IT safety risks, especially in identifying and mitigating the threats to sensitive data or software. Referencing an in-depth guide to DFIR can enhance your risk assessment strategies by introducing practices for identifying digital hazards effectively.
Identifying hazards is the foundational step in risk assessment. You need a clear understanding of what might go wrong to effectively prepare and prevent.
Example: In a manufacturing plant, you might identify hazards such as machinery with unguarded moving parts, slippery floors, or noise pollution.
Step 2. Determine who may be at risk
Next, you determine who is at risk. While this may seem simple, it’s essential to dig deeper than those who may be immediately at risk.
For instance, the obvious victims of a cybersecurity attack would be the business itself. However, customers and suppliers could also be affected and have their sensitive data stolen. If your company has adopted the cloud to store data and run applications, consider protecting these assets by using a Cloud Workload Protection Platform (CWPP) and following data loss prevention best practices to keep your digital environment secure.
When conducting a workplace inspection to identify safety hazards, you might think about the employees who could be injured. But if a potential client were touring your facilities, they would also be at risk.
Identify anyone who could be in danger of an illness, injury, or loss.
Example: For the manufacturing plant, employees working directly with the machinery are at risk of physical injuries like lacerations or hearing loss from noise exposure. Office staff might not be exposed to machinery risks but could be affected by poor ergonomic setups.
Step 3: Evaluate the Risks
You already have your first two questions: what is the hazard? And who is at risk?
Next up is to assess the extent of the risk associated with each hazard. This means considering the likelihood that the hazard will cause harm and the severity of that harm. Then, decide on the preventive measures that can mitigate these risks.
Why It’s Important: Evaluating risks helps prioritize risk management efforts based on the severity and likelihood of negative outcomes. This step ensures that resources are allocated effectively to where they are needed most.
Example: The risk of slipping on the factory floor might be high likelihood but low severity, leading to minor injuries, whereas the risk of an accident from unguarded machinery could be lower likelihood but high severity, leading to serious injuries or fatalities.
Step 4: Record Your Findings
You already have your first two questions: what is the hazard? And who is at risk?
Next up is to assess the extent of the risk associated with each hazard. This means considering the likelihood that the hazard will cause harm and the severity of that harm. Then, decide on the preventive measures that can mitigate these risks.
Why It’s Important: Evaluating risks helps prioritize risk management efforts based on the severity and likelihood of negative outcomes. This step ensures that resources are allocated effectively to where they are needed most.
Example: The risk of slipping on the factory floor might be high likelihood but low severity, leading to minor injuries, whereas the risk of an accident from unguarded machinery could be lower likelihood but high severity, leading to serious injuries or fatalities.
Step 5: Implement Risk Control Measures
What to Do: Once you have identified the necessary risk controls, the next step is to implement them. This could involve training employees, investing in safety equipment, changing processes, or a combination of these. For digital security, setting up a VPN Custom DNS can add an extra layer of protection by preventing access to malicious websites and enhancing network privacy.
For digital hazards, consider training staff to apply the SLAM method whenever they receive suspicious emails, and invest in email security tools that filter out potential phishing attempts.
Why It’s Important: Implementation is where risk assessment leads to practical actions that enhance safety and efficiency in your operations.
Example: Install machine guards, provide personal protective equipment (PPE) like earplugs for noise hazards, implement consistent maintenance scheduling to keep equipment in safe working order, and implement regular safety training sessions.
Step 6: Review and Update the Assessment Regularly
What to Do: Regularly review the risk assessment to ensure it remains up to date with any changes in the workplace, technology, or external environment. Make updates where necessary, especially if new hazards become evident.
Why It’s Important: Continual review and updating ensure that the risk assessment evolves with the operation and continues to provide effective risk management.
Example: After installing new machinery in the plant, the risk assessment is updated to include any new hazards this equipment might introduce, ensuring that the latest safety protocols are in place.
HR risk assessments
Human resources risk assessments seek to handle various potential issues that may arise with a company’s employees.
HR Risk Assessments are also a prime example of looking at risks from different perspectives. HR Risk assessment could be related to employees attempting to abuse benefits or preventing theft of company items.
More often, however, it’s about retaining quality employees, creating a happy, healthy work environment, and improving the hiring process.
50 HR risk assessments example questions:
Creating effective HR assessments can greatly improve the hiring process, employee development, and overall workplace environment. Here are 50 example questions that can be included in various HR assessments to evaluate different aspects of a candidate’s or employee’s competencies, attitudes, and performance:
General and Behavioral Questions
- Can you describe a challenging work situation and how you handled it?
- What motivates you to come to work every day?
- How do you manage stress in the workplace?
- Can you provide an example of how you have worked effectively under pressure?
- Describe a time when you had to deal with a difficult colleague.
Competency Questions
- How do you prioritize your tasks and manage your time?
- What strategies do you use to maintain effective communication in your team?
- Can you give an example of a successful project you led?
- What steps do you take to ensure quality in your work?
- Describe how you approach making a critical decision.
Leadership and Management Questions
- How do you motivate your team?
- Describe your leadership style.
- What do you consider the most challenging aspect of being a manager?
- How do you handle underperforming employees?
- What techniques do you use to manage team conflicts?
Teamwork and Collaboration Questions
- How do you contribute to creating a team-oriented environment?
- Can you share an experience where you had to collaborate with a team to achieve a goal?
- What role do you typically play in team projects?
- How do you handle a situation when a team member is not contributing?
- Describe a time when you helped resolve a dispute among team members.
Cultural Fit Questions
- What do you know about our company culture?
- How do you align with our company’s values?
- What makes you a good fit for this company?
- Can you describe an organizational culture in which you thrived?
- How do you adapt to changes in the workplace?
Problem-Solving Questions
- Describe a time when you identified a potential problem and resolved the issue before it became urgent.
- How do you evaluate the effectiveness of your solutions?
- Can you give an example of an innovative approach you used to overcome an obstacle?
- What steps do you take to analyze a problem before making a decision?
- How do you involve others in the problem-solving process?
Performance Evaluation Questions
- What are your most significant achievements in your current role?
- How do you measure success in your job?
- Can you discuss your most recent performance evaluation?
- What goals have you set for the next year?
- How do you seek feedback to improve your performance?
Career Aspiration Questions
- Where do you see yourself in five years?
- What are your long-term career goals?
- How do you plan to achieve your career objectives?
- What skills are you currently developing?
- How does this position fit into your career path?
Adaptability Questions
- Describe a time when you had to adapt to a significant change at work.
- How do you handle new systems or processes?
- Can you give an example of how you have embraced new technologies in the workplace?
- What do you do when you face an unexpected challenge?
- How quickly do you adapt to new roles or responsibilities?
Communication Skills Questions
- How do you ensure your messages are clear and understood?
- Give an example of how you handled a communication breakdown.
- What communication tools do you find most effective?
- How do you approach delivering difficult messages?
- How do you receive and incorporate feedback?
These questions can be tailored and combined in various ways to create a comprehensive HR assessment tool for different positions and purposes, helping to ensure that you’re not only choosing the right candidates but also fostering growth and development within your team.
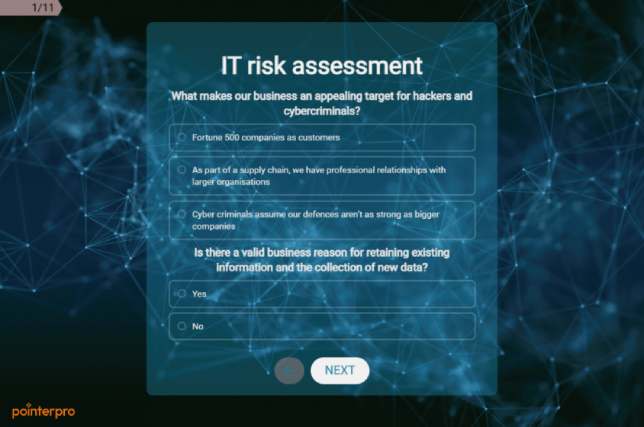
Cyberattacks have been grabbing headlines the past few years, with damages expected to reach $6 trillion in the U.S. in 2021.
Cyberattacks also have a domino effect. Besides any initial losses regarding hardware, systems, laptops, customer data, or intellectual property, companies also face bad press, loss of customer trust and loyalty.
IT risk assessments seek to identify potential weak points in a company’s cybersecurity and predict potential losses. To strengthen this process, reviewing a detailed vulnerability management document can help uncover system weaknesses and prioritize which security gaps need immediate action, such as the implementation of synthetic monitoring.
50 IT risk assessment examples questions
Possible IT risk assessment questions are:
- Is our insurance against cyberattacks adequate?
- Are we prepared for regulatory enforcement and lawsuits?
- How current, complete, and tested in our data breach incident plan?
- Are we using industry best practices against cyberattacks?
- Are there enough training resources available for our employees to spread awareness about data security and risks?
Conducting an IT risk assessment involves identifying and analyzing potential risks that could impact information technology systems and the data they handle. This also includes evaluating how effectively systems are tested for vulnerabilities using trusted penetration testing tools. Here are 50 example questions that could guide you in performing a thorough IT risk assessment:
General IT Environment
- What is the organizational structure of the IT department?
- How are IT policies communicated across the organization?
- What are the current IT projects and initiatives?
- Are there documented and tested disaster recovery and business continuity plans?
Hardware and Software
- What hardware devices are critical to business operations?
- Is there a complete inventory of all IT assets?
- Are software licenses up to date and compliant with legal standards?
- How frequently are patches and updates applied to systems?
Security Measures
- What cybersecurity measures are currently in place?
- Are firewalls and antivirus software installed and regularly updated?
- How are data encryption protocols managed?
- Are there regular security audits and penetration tests conducted?
Data Management
- How is sensitive data identified and classified?
- Who has access to critical data?
- Are data access logs reviewed regularly?
- What measures are in place to ensure data integrity?
User Access Controls
- How are user access rights assigned and managed?
- Are there controls for administrative access?
- How often are access privileges reviewed and updated?
- Are multifactor authentication methods in use?
Network Security
- How is network security monitored?
- Are there any recent network security incidents?
- What is the response plan for a network security breach?
- How secure are the wireless networks?
Incident Response
- Is there an incident response plan in place?
- How are IT incidents detected and reported?
- What is the average response time for an incident?
- Are incident response drills conducted regularly?
Third-Party Services
- What third-party services are used (cloud providers, SaaS, etc.)?
- How are these third-party services evaluated for security?
- Are there contracts and SLAs that include security requirements?
- How is third-party access managed?
Compliance and Legal
- What regulatory requirements are applicable to the IT systems?
- How is compliance with these regulations assessed?
- Are there regular compliance audits conducted?
- What are the legal implications of a data breach?
Physical Security
- How secure are the physical locations of critical IT infrastructure?
- Are access controls in place for sensitive areas?
- Is there surveillance and monitoring at these locations?
- How are physical security breaches handled?
Mobile and Remote Access
- How is mobile device security managed?
- Are there policies for remote access to the network?
- How are personal devices secured for work use?
- What are the security protocols for remote work?
Backup and Recovery
- What backup processes are in place?
- How often are backup integrity checks performed?
- What is the recovery time objective for critical systems?
- Are backups stored securely and off-site?
Employee Training and Awareness
- Is there an ongoing cybersecurity training program?
- How are employees tested on their security awareness?
These questions are designed to uncover vulnerabilities and ensure that all aspects of IT risk are considered. Each question helps to focus on different areas of IT risk, from hardware and software to policies and procedures, ensuring a comprehensive approach to risk management. Staying informed about the latest developments in App & Cloud Sec alternatives can also support a well-rounded risk assessment strategy by highlighting emerging security solutions.
Work safety risk assessments
A work safety risk assessment is a systematic process used by organizations to identify potential hazards in the workplace, evaluate the risks associated with those hazards, and determine appropriate ways to eliminate or control those risks. The main goal of conducting a work safety risk assessment is to ensure the safety and health of employees and to prevent workplace accidents and injuries.
Key Components of a Work Safety Risk Assessment:
-
Hazard Identification: This involves spotting things that could potentially cause harm in the workplace. Hazards can be physical (like machinery), chemical (such as toxic substances), biological (including bacteria and viruses), or ergonomic.
-
Risk Evaluation: After identifying the hazards, the next step is to understand the likelihood of harm occurring and the severity of its impact. This helps in prioritizing which risks need to be addressed immediately and which can be monitored over time.
-
Risk Control Measures: Once risks are evaluated, appropriate control measures are determined and implemented to mitigate or eliminate the risks. This might include engineering controls, administrative controls, workplace policies, or personal protective equipment.
-
Recording and Reporting: It’s important to document the findings of the risk assessment. This documentation should include details about the hazards identified, their associated risks, and the decisions made regarding control measures.
-
Review and Update: Risk assessments should not be static; they need to be reviewed and updated regularly to ensure they remain effective and take into account any changes in the workplace, such as new equipment, processes, or changes in personnel.
The process is crucial for maintaining a safe work environment and is often required by law in many jurisdictions. Employers are responsible for carrying out these assessments and implementing the recommended safety measures. By doing so, they not only comply with legal obligations but also contribute to creating a safer, healthier workplace. This proactive approach helps in reducing the likelihood of accidents and associated costs, while also promoting a culture of safety among employees.
50 work safety risk assessments example questions
Creating a thorough work safety risk assessment is critical in ensuring a safe workplace. Here are 50 questions that can guide the risk assessment process across various workplace scenarios:
General Work Environment
- Are emergency exits clearly marked and easily accessible?
- Is the lighting adequate in all work areas?
- Are floors clean and free of hazards that could cause slips, trips, or falls?
- Is there a process in place for regularly reviewing and updating safety policies?
- Are all employees aware of the location of first aid kits and how to use them?
Equipment and Machinery
- Are all machines and equipment regularly maintained and inspected?
- Do employees receive proper training on each machine they are required to use?
- Are safety guards in place on all necessary machinery?
- Is there a protocol for reporting and addressing equipment malfunctions?
- Are proper lockout/tagout procedures in place and followed?
Chemical and Material Handling
- Are Material Safety Data Sheets (MSDS) available for all hazardous substances?
- Is proper personal protective equipment (PPE) provided and used when handling hazardous materials?
- Are all chemicals clearly labeled and properly stored?
- Is there adequate ventilation in areas where chemicals are used?
- Are spill containment and cleanup procedures in place and known to all employees?
Fire Safety
- Are fire extinguishers easily accessible and regularly inspected?
- Do employees know how to use fire extinguishers effectively?
- Are smoking and open flames appropriately controlled in all areas of the workplace?
- Is there a regular schedule for testing fire alarms and smoke detectors?
- Are flammable materials stored safely and securely?
Employee Training and Awareness
- Are all new employees given a thorough safety orientation?
- Is ongoing safety training provided to employees?
- Are employees trained on the specific risks associated with their job duties?
- Is there a system in place for employees to report safety concerns anonymously?
- Are supervisors trained to recognize safety hazards and respond appropriately?
Ergonomics
- Are workstations ergonomically designed to prevent strain and injuries?
- Do employees receive training on proper ergonomics practices?
- Is there regular assessment of ergonomic practices and equipment?
- Are adjustable chairs and desks available for employees who require them?
- Are employees encouraged to take regular breaks to prevent repetitive strain injuries?
Environmental Concerns
- Is there an assessment of the environmental impact of work practices?
- Are efforts made to reduce environmental harm from work processes?
- Are employees trained on environmental policies relevant to their work?
- Is there a protocol for handling and disposing of environmentally hazardous substances?
- Are there measures in place to minimize noise pollution?
Health and Welfare
- Is there a policy in place to handle workplace incidents and injuries?
- Are there resources available for employee mental health and wellbeing?
- Is there easy access to drinking water and clean restrooms?
- Are employees encouraged to report health and safety issues?
- Are there health screenings available for employees in high-risk jobs?
Accident and Emergency Response
- Is there a clear procedure for responding to workplace accidents?
- Are records kept of all incidents and accidents in the workplace?
- Are emergency contact numbers clearly displayed?
- Are regular drills conducted for possible workplace emergencies?
- Is there a designated safety officer or first aid responder on site?
Regulatory Compliance
- Is the workplace compliant with all local, state, and federal safety regulations?
- Are there periodic reviews to ensure continued compliance with safety laws?
- Is there documentation proving compliance with safety standards?
- Are safety audits conducted by external inspectors?
- Is there a process for addressing any non-compliance issues identified during audits?
These questions help establish a baseline for identifying potential risks and ensure that all aspects of workplace safety are addressed, leading to a safer and more compliant environment for all employees.
Now that you’ve analyzed and evaluated your company’s risks, it’s to prioritize these risks.
There are two key factors: probability – the odds of the risk happening- and impact – the effect of the risk.
With these parameters, you can build your risk matrix:
Consider these two parameters for each risk. Risks that score high in both categories will be the ones you should tackle first.
Whether a risk is categorized as low, moderate, high, or extreme shouldn’t be left up to chance, though.
By adding a score or value to each answer option in your assessment, you can have the risk assessment calculate each risk for you and show you an outcome or final screen containing the most urgent risks or, alternatively, define the appropriate category for each potential risk. You’ll need risk assessment software with features that allow custom scoring and multiple outcomes. Luckily, Pointerpro has such features. Here are two help guide videos, just to give you a quick glimpse.
Assessing risks is only half the battle. With Pointerpro, you can build a risk assessment that automatically generates a detailed risk report, containing tailored advice on how to mitigate the risks. This is often used by consultants and professional service companies to make their audience aware of the importance of a specific set of risks. An IT security consultancy for example can use a cyber risk assessment for its prospects to identify security vulnerabilities and advise how to address these.

Want to know more?
Subscribe to our newsletter and get hand-picked articles directly to your inbox